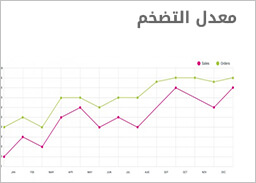
اخبار البنك المركزي
- جديد
- جديد
- جديد
- جديد
- جديد
- جديد
- جديد
- جديد
احدث وظائف البنوك



Prime Relationship Manager
وظائف البنك المصري الخليجي - EG Bank
الخميس 13 ديسمبر 2018
مشاهدة الوظيفة

MINT Customer Relationship Officer
وظائف البنك المصري الخليجي - EG Bank
الخميس 13 ديسمبر 2018
مشاهدة الوظيفة
احدث وظائف الشركات
البنوك المصرية
- البنك المركزي المصري
- البنك الاهلي المصري
- بنك مصر
- بنك القاهرة
- بنك الاسكندرية
- بنك التعمير والإسكان
- المصرف المتحد
- بنك فيصل الاسلامي
- البنك الزراعي المصري
- بنك قناة السويس
- بنك CIB - سي اي بي
- بنك HSBC - اتش اس بي سي
- بنك QNB - قطر الوطني
- البنك العربي الافريقي الدولي - AAIB
- بنك الامارات دبي الوطني - NBD
- البنك الأهلي الكويتي - ABK
- بنك عودة
- البنك الأهلي المتحد
- البنك العربي
- بنك المشرق